Hacker Community
Flipper Zero Transmits APRS With No Extra Parts – Hackaday (Hackaday)
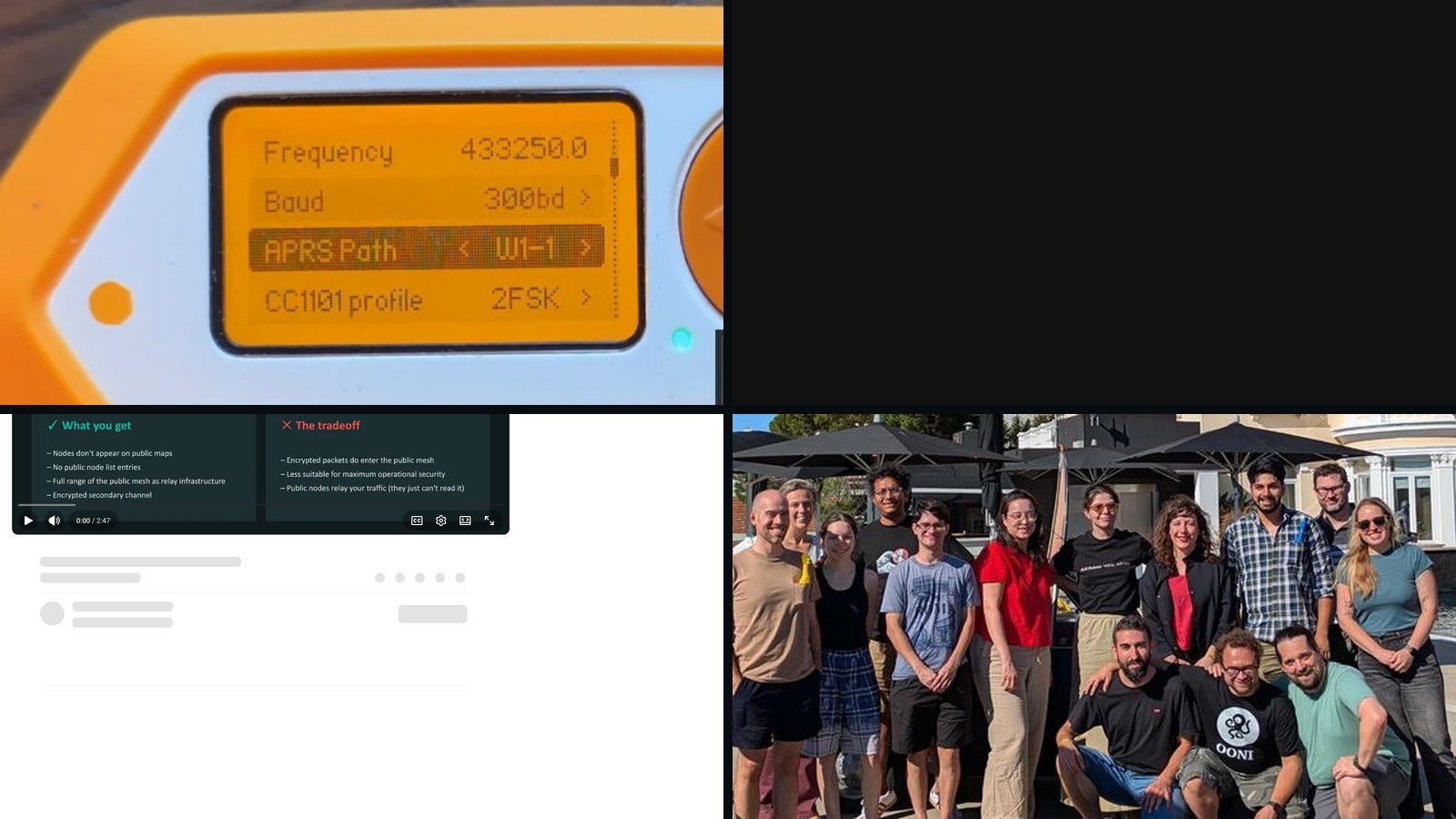
Summary: A developer has modified the Flipper Zero, a popular RF hacking tool, to transmit APRS (Automatic Packet Reporting System) data without requiring any external hardware. This is achieved by exploiting the device’s existing 435 MHz ISM band radio and using software to approximate the necessary FM modulation via FSK. While the signal may not be compatible with all standard APRS receivers, it represents a significant reduction in the barrier to entry for creating a portable, low-cost APRS beacon.
Why it matters: This demonstrates the continued evolution of the Flipper Zero from a discrete tool into a flexible, software-defined radio platform, lowering the cost and complexity threshold for amateur radio experimentation and expanding its utility in field operations and emergency communications prototyping.
Context: APRS is a foundational amateur radio protocol for location tracking and messaging. The Flipper Zero community has a history of pushing the device beyond its marketed capabilities, often repurposing its hardware for unintended RF applications, which blurs the line between consumer hacking tools and specialized radio gear.
"The Flipper Zero RF hacker’s multi tool normally needs to be hooked up to an external transmitter to do APRS, but [Richard YO3GND] has made his Flipper do the job without any external parts at all." — HACKADAY
Commentary: This is a tool-release signal with a cypherpunk infrastructure angle: it further weaponizes a consumer device for decentralized, off-grid communication. The hack reduces the logistical footprint for ad-hoc mesh networking, which has implications for disaster response, activism, and counter-surveillance ops. However, the non-standard modulation also highlights the technical debt and compatibility trade-offs inherent in these repurposing efforts, creating a parallel, slightly incompatible network layer.
Date: April 21, 2026 12:00 AM ET
URL: https://hackaday.com/2026/04/21/flipper-zero-transmits-aprs-with-no-extra-parts/
AI Sentiment Score: Negative (80%)
AI Credibility Score: 9.9/10 — High
Scores and text generated by AI analysis of the source article indicated.Year in Review: OONI in 2025 (Ooni)
Summary: The Open Observatory of Network Interference (OONI) has shifted its public-facing strategy from a generalized measurement platform to a thematic, event-response model. In April 2025, it launched dedicated OONI Explorer pages for tracking blocks of social media, news media, and circumvention tools, bundling short reports, long-form research, and real-time charts. This operational pivot is paired with targeted outreach, including a workshop for Forus’s global civil society network and a community-driven research project in Taiwan facilitated by the Open Culture Foundation.

Why it matters: It signals a maturation of censorship measurement infrastructure from data collection to actionable intelligence, directly arming activists and researchers with curated, context-specific evidence.
Context: This reflects a broader trend in the digital rights space where toolmakers are moving beyond providing raw data feeds to building interpretative layers and fostering localized, sustainable measurement communities.
"OONI Probe is a free and open source tool that we have built since 2012, designed to measure various forms of internet censorship. To enable communities worldwide to run OONI Probe and." — OONI
Commentary: This is a cypherpunk infrastructure signal evolving into a village/workshop pipeline. The thematic pages operationalize data for rapid response, lowering the activation energy for evidence-based advocacy. The partnership with OCF in Taiwan exemplifies a model for embedding measurement tools within local civil society, creating a more resilient and distributed detection network against state-level filtering.
Date: April 27, 2026 12:00 AM ET
URL: https://ooni.org/post/2025-year-in-review/
AI Sentiment Score: Neutral (50%)
AI Credibility Score: 10.0/10 — High
Scores and text generated by AI analysis of the source article indicated.MNT Reform is an open hardware laptop, designed and assembled in Germany (News.Ycombinator)
Summary: The MNT Reform, an open-hardware laptop designed and assembled in Germany, is being discussed by users as a niche but significant project. It is characterized by its modularity, repairability, and hacker-friendly ethos, though it faces performance and usability trade-offs compared to mainstream options. The conversation highlights its role as a ‘laptop of Theseus’ for enthusiasts and a cultural artifact within the open-hardware movement.

Why it matters: This signals a maturing pipeline for open-hardware consumer electronics, moving from pure ideology to a functional, community-supported product with real-world trade-offs and a dedicated user base.
Context: The open-hardware laptop space is contested between usability-first projects like Framework and ideology-first projects like MNT, with the latter serving as a testbed for long-term repairability and community-driven design.
"I should really write up a long-term review of this thing at some point, but overall I love it. It can be a bit rough around the edges at times, but it’s." — NEWS.YCOMBINATOR
Commentary: MNT Reform operates as a village/workshop signal: it’s a functional prototype for a sustainable, hacker-maintained computing future, but its ARM SoC limitations and boutique nature confine it to a patron class. Its real impact is cultural, proving a market for upgradeable, blob-minimized hardware and providing a blueprint for when mainstream Thinkpads eventually wear out.
Date: April 20, 2026 12:00 AM ET
URL: https://news.ycombinator.com/item?id=47834689
AI Sentiment Score: Neutral (50%)
AI Credibility Score: 10.0/10 — High
Scores and text generated by AI analysis of the source article indicated.Spring, Solder, and Side Quests (Ifixit)
Summary: iFixit’s field report from European maker events reveals a deliberate strategy to convert repair-curious individuals into active contributors. The company uses free tool distribution to solicit community knowledge, observes that hands-on workshops catalyze the ‘I can actually do this’ moment, and confronts a persistent gender gap in perceived technical competence. Notably, they identify smartphone cleaning as a low-barrier gateway to repair, while also grappling with the unintended consequence of their workshops becoming informal childcare.

Why it matters: This is a direct signal of the repair movement’s on-the-ground tactics and cultural friction points, showing how a leading institution operationalizes community growth and confronts adoption barriers.
Context: iFixit’s evolution from a parts retailer to a community platform represents a key pipeline for mainstreaming hacker-world repair practices.
"What sticks with me from the past few months of events isn’t the number of calendar days or the names of the people I’ve met (I’m terrible with names, by the way),." — IFIXIT
Commentary: The report functions as a village/workshop signal, documenting the tangible methods—tool-for-knowledge swaps, gateway maintenance tasks—used to lower activation energy. The explicit gender-based self-dismissal highlights a deep-seated cultural barrier the movement must systematically dismantle, beyond mere tool access. The ‘kid drop-off’ phenomenon, while a logistical challenge, ironically validates the approach’s appeal and underscores the demand for intergenerational technical literacy.
Date: Wed, 22 Apr 2026 06:27:11 +0000
URL: https://www.ifixit.com/News/117025/spring-solder-and-side-quests
AI Sentiment Score: Negative (66%)
AI Credibility Score: 10.0/10 — High
Scores and text generated by AI analysis of the source article indicated.How to Be Invisible on Meshtastic (Youtube)
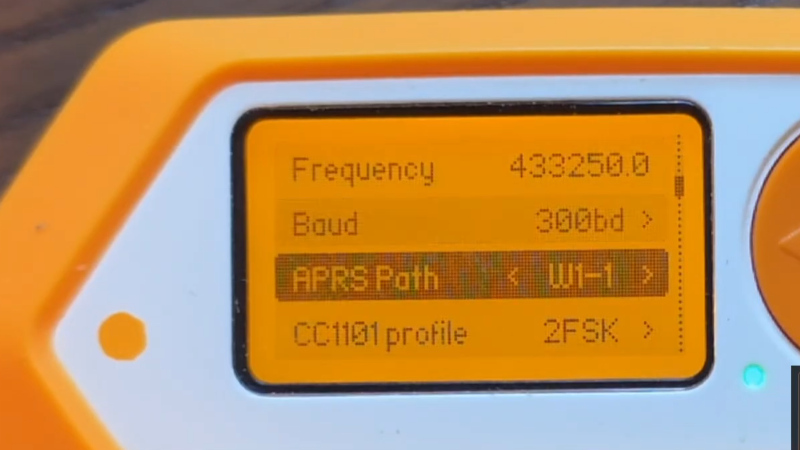
Summary: A technical guide details two operational methods for achieving privacy on the open-source Meshtastic LoRa mesh network. The first creates a fully isolated, encrypted private mesh, while the second uses public infrastructure with hidden nodes and encrypted traffic for extended range. The guide includes specific hardening steps to reduce a node’s radio-frequency and data-leakage footprint.
Why it matters: This represents a concrete, workshop-level signal of operational security practices moving from cypherpunk theory into deployable, consumer-grade hardware, reflecting a maturation of surveillance-resistance tooling.
Context: Meshtastic’s default configuration promotes open, public mesh participation, creating tension for users seeking coordination or communication without public logging or mapping.
"I you need a lower profile, there are two clean methods to keep your nodes off the public map, out of node lists, and communicating privately. Option 1 — Fully Private Mesh:." — YOUTUBE
Commentary: The semi-private model is the more significant archetype: a village/workshop signal of pragmatic threat modeling. It accepts the infrastructural reality of public relays to gain range while implementing client-side opacity, a compromise that will likely define the next wave of consumer privacy tools. This move from total isolation to calculated opacity within public systems indicates a shift from hobbyist tinkering to applied operational security for real-world use.
Date: April 22, 2026 12:00 AM ET
URL: https://www.youtube.com/watch?v=rkiTcCsjID8
AI Sentiment Score: Negative (62%)
AI Credibility Score: 10.0/10 — High
Scores and text generated by AI analysis of the source article indicated.How to Remove MacBook ID Activation Lock by T203 (Ifixit)
Summary: A detailed iFixit guide documents the T203 hardware toolchain for removing the Activation Lock on 2018-2020 T2-chip MacBooks. The process involves physically desoldering the T2 ROM chip, using a specialized programmer seat to write unlock data, and then restoring the device via Apple Configurator 2. This is a hardware-hacking signal, representing a direct, physical countermeasure to Apple’s firmware-level security and ownership controls.

Why it matters: It signals a maturation of the right-to-repair fight into a hardware-level arms race, providing a concrete, documented method to bypass a core Apple security feature that locks devices to an owner’s iCloud account.
Context: Apple’s T2 chip and subsequent Apple Silicon integrate hardware-level security, including Activation Lock, which renders lost, stolen, or second-hand devices unusable without the original owner’s credentials. The repair community has historically sought software bypasses; this represents a shift to required physical intervention.
"- T203 includes two tools: T203 USB flash drive and T203 ROM seat. T203 is mainly used to remove the EFI lock, pin code lock, and bypass the iCloud activation lock of." — IFIXIT
Commentary: This is a village/workshop signal, moving from theoretical discussion to documented, repeatable procedure. It creates a tangible market for specialized tools (T203) and knowledge, directly challenging Apple’s control over device lifecycle. The implication is a bifurcation: legitimate repair shops may adopt this for legitimate unlocks, while it also lowers the barrier for laundering stolen devices, forcing a recalibration of security-versus-ownership debates.
Date: April 20, 2026 12:00 AM ET
URL: https://www.ifixit.com/Guide/How+to+Remove+MacBook+ID+Activation+Lock+by+T203/143072
AI Sentiment Score: Negative (66%)
AI Credibility Score: 10.0/10 — High
Scores and text generated by AI analysis of the source article indicated.Image composite via HACKADAY, OONI